Sales Inquiries: (855) 966-3250
Existing Clients: (866) 644-4005
Cybersecurity Services in Las Vegas
Cybersecurity Services That You Can Trust
In today’s modern world, cybersecurity is a must for any Las Vegas business looking to keep its data safe and operations running smoothly. Whether business or personal, you store your data onto some computer- or cloud-based device to keep it protected. RedPanda Systems delivers personalized cybersecurity services in Las Vegas to safeguard our clients from cyber-attacks, malicious software, and breaches. We have honed our skills for many years, and we use our industry knowledge to protect our clients throughout Las Vegas and surrounding areas. No company expects to get hit by these potential data attackers. Still, at the end of the day, you need the protection of firewalls, security audits, and more from the professional team at RedPanda Systems.
We not only protect your business with our cybersecurity services but your customer’s information as well. Please give them a sense of relief by hiring our staff today and maintain your reputation of offering a safe operation. Not only can we assist with cybersecurity, such as firewalls and security audits, but we offer a plethora of other IT services in Las Vegas. Let our Las Vegas cybersecurity experts shield your business today.
Local Cybersecurity Services Experts Who Understand Las Vegas Businesses
When it comes to protecting your digital assets, you don’t want an out-of-state call center or a faceless vendor. You want a team that understands the fast pace and high stakes of doing business in Las Vegas. At RedPanda Systems, we live and work in the city we serve. As an IT Support company in Las Vegas, our cybersecurity experts are always close by, offering real-time support, local accountability, and on-site service when needed.
Why Cybersecurity Services Are Essential for Las Vegas Companies
Cybersecurity is the protection of networks, data, programs, and other digital systems or devices. RedPanda Systems has been serving Las Vegas companies for years and has all the tools and knowledge required to get the job done. We work efficiently to produce cybersecurity systems built for anything you need protecting. Over the years, we have helped many different companies and constructed unique solutions when they need assistance. We can help your company save what it holds most valuable by preventing attacks from hackers and malicious programs designed to infiltrate and steal your information, money, and more. Our comprehensive cybersecurity services in Las Vegas include all of the following:
Cyber Security Assessment Services
Cyber Security Consulting Services
Cyber Security Monitoring
Cyber Security Support Services
Cyberattacks don’t just happen to big corporations. In fact, small and midsize businesses are increasingly targeted. Whether you're in hospitality, healthcare, law, finance, or retail, protecting sensitive data is critical. Our cybersecurity services in Las Vegas help businesses comply with industry regulations, maintain customer trust, and prevent costly downtime due to breaches or malware.
Ransomware attacks
Phishing scams
Insider threats
DDoS (Distributed Denial of Service)
Unpatched software vulnerabilities
Weak firewall or network configurations
Is Your Cybersecurity Strategy Strong Enough for Cyber Insurance?
Cyber insurance providers aren’t just looking at your coverage limits—they’re looking at your cybersecurity posture. If you can’t show that you’ve taken the right steps to protect your systems and data, you may face higher premiums, exclusions, or even denial of coverage.

Within our Cybersecurity Services in Las Vegas, RedPanda Systems offers cybersecurity assessments specifically designed to help businesses meet evolving cyber insurance requirements. We evaluate your current protections, identify any gaps, and help you put the right safeguards in place—before your insurer demands them.
Our assessments include:
A full audit of your cybersecurity environment
Gap analysis against common insurance benchmarks
Clear, actionable steps to strengthen your position
Documentation to share with insurance providers
Whether you're applying for cyber insurance for the first time or preparing for renewal, our team will ensure your business is protected—and properly represented.
What Clients Say About Us
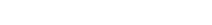
Want to see your Score? Get it in 30 seconds!
Core Cybersecurity Services We Offer in Las Vegas
Our comprehensive Las Vegas cybersecurity services are customized to your exact needs. We don’t just install tools—we create a secure IT environment that evolves with your business. Here are a few of the core services we offer:
01
Cybersecurity Assessments & Security Audits
We evaluate your current defenses, identify gaps, and provide a clear, actionable roadmap to close them—before cybercriminals find and exploit them.
02
Managed Firewall Services
We design, configure, and proactively manage firewalls to ensure your network is fully protected against intrusion, malware, and data leaks.
03
Cybersecurity Monitoring & Incident Response
Our real-time monitoring solutions detect threats early—before they escalate. If an incident occurs, we respond quickly and effectively to contain it.
04
Cybersecurity Consulting Services
Need a cybersecurity strategy tailored to your industry or compliance requirements? Our experts will help you build and implement a plan that works.
05
Employee Security Awareness Training
Phishing attacks often target your staff. We train your team to recognize and report suspicious activity, creating a human firewall that’s just as strong as your tech.
What is Cybersecurity—and Why It Matters
Cybersecurity is the process of defending your digital systems, networks, and data from unauthorized access or damage. As a leading provider of cybersecurity services in Las Vegas, RedPanda Systems takes a proactive approach to protection. We combine advanced monitoring, threat detection, and firewall management with personalized support that adapts to your industry and infrastructure.
Whether you operate in a regulated sector or simply want to strengthen your cyber posture, we offer solutions that scale with your business.
Long-Term Protection Starts with a Conversation
Your business deserves a cybersecurity partner, not just another service provider. At RedPanda Systems, we pride ourselves on building long-term relationships and delivering peace of mind through dependable cybersecurity services in Las Vegas.
We’re here when you need us. No hard sells. Just expert protection from a team that knows Las Vegas inside and out.
That’s why we tailor our solutions to fit your unique needs, ensuring your business stays secure, compliant, and ahead of evolving cyber threats.
How Firewalls Protect Your Business from Threats
When dealing with cybersecurity, you may hear the term firewall. While not as visually appealing as it sounds, this piece of protection will be one of your greatest safeguards when protecting your systems and devices from outsiders. A firewall is a network security device designed to monitor incoming and outgoing network traffic. They block or permit data packets based on the strict set of rules you have us implement based on your unique needs. As part of our Cybersecurity Services in Las Vegas, we will construct these firewalls in your system to make your hardware and software impenetrable. We provide each client with comprehensive firewall management in Las Vegas to give them peace of mind after we have left. By staying up-to-date on all the latest technology and advancements, we can offer modern solutions for modern problems. Below are the three types of firewalls we use:
Next-generation firewalls (NGFW)
Proxy firewalls
Network address translation (NAT) firewalls
Stateful multilayer inspection (SMLI) firewalls
Why Run Cybersecurity Audits and Assessments ?
Cybersecurity Services in Las Vegas: Providing Effortless IT Relocation Without Interrupting Your Workflow
RedPanda Systems also provides cybersecurity audits and assessments in Las Vegas to prevent clients from becoming outdated and find holes in the operations. The checks are necessary the same way you run a periodic examination on your car’s operating system or as you would go to the doctor for a checkup. Cybersecurity audits allow our team of professionals to catch small issues before cybercriminals gain access to your system and precious data. Businesses with little to no security and known leaks aren’t as likely to attract customers. We help you stay in business and maintain your reputation.
There are plenty of different cybersecurity threats out there, and sometimes they can be sneaky. Employees need to be made aware of phishing scams, malware, and more. They can accidentally permit thieves disguised as an unsuspicious email or update. Our regular audits and assessments help keep those criminals at bay. We can also help educate your staff to prevent them from falling for these traps and tricks.
Benefits of Subscribing to our Cybersecurity Services Plan in Las Vegas
When looking for a cybersecurity team for your business, you need a group of technicians who instill confidence in their work. At RedPanda Systems, we build a strong relationship built on our clients’ ability to trust our knowledge, skill, and suggestions when implementing Cybersecurity Services in Las Vegas on all devices and systems. By joining our Las Vegas cybersecurity plan, you can ensure we will always be there when you need us most. With professional installations paired with regular maintenance checks, you can be sure your systems and information have the highest degree of cybersecurity protecting them.
Cybersecurity Services in Las Vegas: Built for the Speed and Security Needs of Las Vegas
Whether you're a law firm storing confidential documents, a medical provider safeguarding patient records, or a casino with large volumes of customer data, our cybersecurity services in Las Vegas are built with your needs in mind.
We support high-demand industries, including:
Healthcare & Medical Practices – HIPAA-compliant cybersecurity
Law & Finance – Data confidentiality and regulatory compliance
Hospitality & Events – Fast-response network security
Startups & SMBs – Affordable, scalable cybersecurity packages
Book Your Appointment With RedPanda Systems Today
When you are ready to launch your company or have suffered a recent attack on your data and information systems, give RedPanda Systems a call. We provide the most detail-oriented cybersecurity services in Las Vegas possible to protect not only you but your customers. Rely on us to prevent cybercriminals from breaking into your company by installing firewalls and working directly with your systems to ensure success.
Experience Wildly Reliable IT in Las Vegas
Partner with RedPanda Systems for IT Services in Las Vegas that save time, cut costs, and drive revenue. Let us align your technology with your goals to ensure seamless business operations and growth.
Call (855) 966-3250 today or click on the button below to fill out a form to schedule your appointment, and start achieving your business goals.